Warning: This challenge is still active and therefore should not be resolved using this information.
Aviso: Este reto sigue en activo y por lo tanto no se debería resolver utilizando esta información.
CanYouHack.it Mobile2 Challenge – Follow The Web (English)
Intro
This crackme is for the challenge Mobile 2 of canyouhack.it.
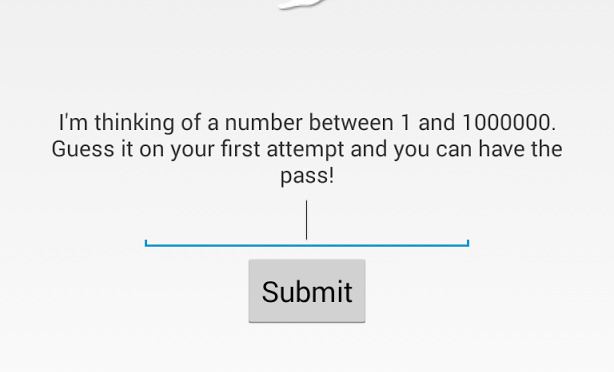
This time you need to understand how the crackme works over the web.
Decompiling
The crackme is given again at Google Play, so the first step is to install and recover the APK for decompiling. The latter, I leave to you.
Open the victim with APK Studio and view the content of Mobile2.java

First we view one link:
http://canyouhack.it/Content/Challenges/Mobile/2/index.php

If we go to the link, we view one string like a hash: 68a571bcf7bc9f76d43bf931f413ab2c. Umm, it’s like MD5. Go to decrypt online and we get the pass: «canyouhack.it». But if we test this password in the crackme, surprise!, nothing happens. We need to continue analyzing the code. Later we view the next interesting link:
«http://canyouhack.it/Content/Challenges/Mobile/2/submit.php?Token=» + Mobile2.token + «&Attempts=»
The program submit one token and concatenate with the number of attempts. Ok but what is the token and what is the number of attempts?
In this point we have to try with the information we already have.
Testing with the link of bottom we get “Nice try!” message.
http://canyouhack.it/Content/Challenges/Mobile/2/submit.php?Token=68a571bcf7bc9f76d43bf931f413ab2c&&Attempts=0
Testing with the link of bottom we get “Very Good, the password is Top*****!” message.
http://canyouhack.it/Content/Challenges/Mobile/2/submit.php?Token=68a571bcf7bc9f76d43bf931f413ab2c&&Attempts=1